Week 1 of the AfterChallenge
By Christopher Mohr
There is a scam circulating around Japan in the form of official-looking websites that themselves warn about scams, in other words, a scam page promoting anti-scam practices. The attackers behind this campaign have cleverly found a way to use their targets’ vigilance as an attack surface.
Phishing Page Warning Japanese Citizens of Special Fraud Scams (Source: Hybrid-Analysis.com, because drive-by attack techniques were detected the malicious URL in the browser has been redacted)
A Common Japanese Scam
Some background information is helpful to provide context:
A common scam in Japan is called Ore Ore Sagi or It’s me! It’s me! The scammer calls the target pretending to be a relative in some sort of trouble (accident, arrested and jailed etc.) and needing a money transfer ASAP to resolve the matter or get bailed out. The target is usually an elderly person who’s likely to be less tech savvy and have some money saved.
A “cold reading” tactic used to gain sympathy often accompanies this scam. The caller starts by saying something like, “It’s me, I’m in trouble”. The target says, “Is that you, Joey?” to which the caller replies, “Yeah, it’s Joey”. Lost in the panic and urgency of this fake crisis, the victim has unwittingly provided info to the attacker to advance the scam along.
Data from Japan’s National Police Agency suggests a dramatic rise in the of Ore Ore Sagi cases between 2024 and 2025, both in total number and as a percentage of total special fraud cases.
Special fraud, or tokushu sagi, is a term used in Japan to describe fraud committed online or over the phone instead of face to face.
In 2024, Ore Ore Sagi cases made up 6,752 out of 21,043 special fraud cases, about one-third (32.1%) of total cases.
Earlier I used the word, “suggests” because the 2025 data was provisional at the time of this writing. However, if these provisional numbers are close to the finalized values, it paints a picture of a disturbing trend: Ore Ore Sagi made up 14,393 of 27,758 special fraud cases that year, over half the total (51.9%). While this may be one of the ‘oldest tricks in the book’ in Japan, it’s apparently an effective one.
It was important to bring up Ore Ore Sagi, because of the long history of its use and the recent uptick in cases and its connection to the phishing page. This is a major problem in Japan to the point that legislation was passed to reduce the problem.
Osaka passed a law that went into effect on 1 August 2025 banning individuals age 65 or older from using an ATM while on a cellphone. The legislation also requires banks to run awareness campaigns informing their customers of the new regulation.
The public, government, and news media in Japan seem to have become more vigilant about Ore Ore Sagi, but it is precisely this vigilance that this scam campaign uses to lure its victims into a scam.
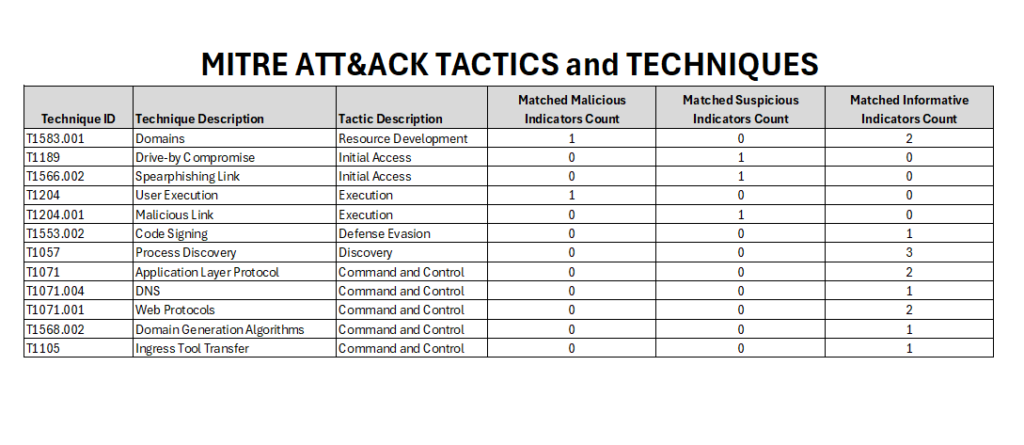
MITRE ATT@CK TACTICS and TECHNIQUES provided by Hybrid-Analysis tell a lot about this campaign without the risk of ‘detonating’ it on a home system lacking adequate sandbox protections
How Victims Were Likely Targeted
In past Malware Monday articles about phishing attacks, I was the target, so I knew how it started.
In this campaign, I don’t have such firsthand knowledge; I found this scam by looking at reports at the Hybrid-Analysis website. One of its reports included the MITRE table above. It’s a great resource for examining this attack.
One technique used was T1566.002 Spearphishing Link; this was a targeted campaign, not a bulk one.
So how was the target list created? We can only speculate. One possibility is that the list came from recent data leaks. In 2024, the Japanese government suffered 447 attacks, almost double the previous year’s total.
Other recent data breaches in 2025 like the DIC Utsunomiya Central Clinic breach (300K customers), Sankei Lingerie (292 K customers), and Sompo Japan Insurance (7.3 M customers) would have provided scammers a list of millions of potential victims.
Given the sophistication of this campaign it’s also conceivable that a list came from previous phishing campaigns, which would have tracked which email addresses worked and who was responsive.
The main webpage captured from the scam campaign site discusses Ore Ore Sagi, refund fraud, investment fraud, and online fraud as top telecom fraud schemes. This is the psychological element of the page’s content; who are the attackers trying to get to react to this content? From a social engineering standpoint, the content suggests it’s most likely designed to induce elderly people to respond.
Maybe the online fraud targeted some younger demographics because of romance scams, but the rest of these campaigns would seem more effective against people who were less tech savvy and had money. That says “elderly people” to me, but in fairness, I am speculating.
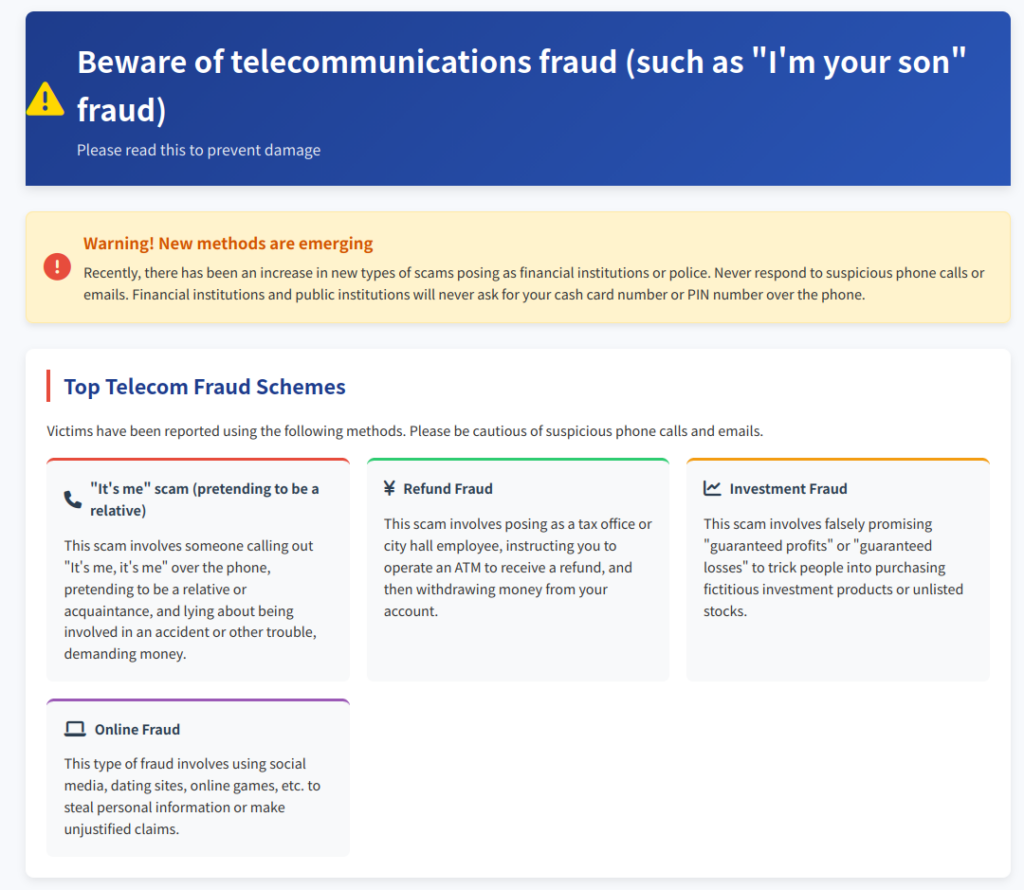
(Above) an English translation of one of the pages taken from URLScan.io
How the Attack Probably Worked
Drive-Bys, Malicious Links, C2, and Domain Generation
We know so far that the victims were targeted, and we have speculated on the target demographic, but unfortunately we cannot say for sure or with much certainty whether the phishing appeared on mobile or desktop devices.
T1189 is a drive-by compromise technique, so just visiting the site is risky. This is why the page’s URL was redacted in the earlier screenshot from Hybrid-Analysis.
It is also why I have removed scripting (which included links) from the original URLScan.io page capture, which is in Japanese and the English translation of that content. It would be irresponsible on my part to put readers at risk of attack. You may click the links to examine ‘de-fanged’ versions of these pages.
The page uses defense evasion to make it hard for scanners to learn its characteristics. Process discovery is the page looking for security tools and antivirus software. This is simply the attackers trying to prevent defenders from detecting malware and from researching how their attack campaign works.
Several command and control (C2) tactics were listed in the MITRE table. This configures the victim’s machine to ‘phone home’ to a server that issues commands. Once this command structure is in place, the sky’s the limit in how much damage can be inflicted.
User execution was listed as a technique, meaning that some elements of the attack required input from the user. This probably would have come from the links that were removed, which were in the section of the page where reporting hotlines were listed.
The target receives a message inducing them to click on one of the hotline numbers. Maybe they were worried about a scam, maybe they wanted to report an incident. Either way, they are hooked at this point. The psychology of how this page played on its targets’ vigilance to lure them into another attack is probably the attack’s biggest strength.
Another feature of the scam page appears in T1568.002, Domain Generation Algorithms (DGA) and further demonstrates sophistication on the part of the attackers. With DGA, the C2 server cycles through programmatically-created domain names. It prevents you from blocking this attack by simply blacklisting the first domain you see.
Copyright Section
The copyright section at the bottom was one of those things that made me go ‘hmmm’. Encouraging users to use and modify materials freely for a public service announcement campaign is something you would expect, but it’s contrary to the concept of copyright protection. This appears to be an example of trying too hard to seem authentic.
The script that was removed from the English and Japanese versions of the URLScan.io page capture contained code that sets the ‘last updated’ date in the footer to whatever the current date is at the time the page is loaded. This creates the impression that the page always appears to be a freshly maintained, current official document regardless of when it was actually last updated.
(Above) Copyright notice footer from website translated into English. This raises suspicion because a public service announcement by its nature does not contain proprietary information that one would want or need copyright notices to protect. It is missing a ‘Last Updated On <date>’ line because that was in the malicious script removed from the URLScan capture
Unresolved <div> Tags in Header
The header has one or two <div> tags that are unresolved, raising two possibilities: (1) there are two unresolved <div> tags, meaning they have no corresponding closing </div> tag or (2) the second of the two <div> tags is a typo and should be a </div> tag instead.
Without any other evidence, I am inclined to go with (2). It’s more likely that whoever wrote this code made a typo or maybe had a bunch of nested <div> tags and messed up when deleting them. It’s less likely that something technically sophisticated happened.
Even if something sophisticated did happen, we don’t have enough information to investigate it.
Fighting Back
It’s easy to be disillusioned by the thought that a page that appears to be anti-scam was actually one of the biggest scams of all, but that does not mean you cannot do anything about it. A helpful analogy is the adage that just because you are in a police station, it does not mean that you can’t have your pocket picked. Crimes can happen anywhere; scams can happen on any webpage.
Exercising caution when a link expressing urgency shows up in your messages or inbox is the best first step. Slow down and avoid the knee-jerk reaction to click that link. Always keep in mind that simply going to another page is sometimes enough to activate an attack.
If a message claiming to be from a tax agency, sheriff, utility bill company, bank, broadband provider, etc. tries to get you to do something ASAP, there’s a good chance it’s a con.
This is why I am a firm believer in independent verification. Don’t verify by clicking the link in the message. Instead, remove yourself from that conversation and start a separate conversation with the organization in question to verify if the claims in the original message are true. This takes the scammer out of the equation entirely.
The best response to a scam like Ore Ore Sagi is to provide the caller with a false name: “Is that you, Lenny?”, knowing full well there are no relatives named Lenny in the family. If the caller goes along with being called Lenny, then you know you have a scammer on the line. Keep them on the line and gather as much information as possible to provide to law enforcement.
This scam campaign was fascinating in the psychological tactics it used in appealing to users whose desire to avoid getting scammed actually set them up for another scam. The high potential for malicious activity combined with defense evasion and the ability to detect security software demonstrated sophistication. Until you have the right sandbox setup, it’s best to keep some distance from these malicious sites, even though one may be curious about them.
Sources:
Japan National Police Agency, JNPA Specialized Fraud Statistics: hurikomesagi_toukei.xlsx
NOTE: The next two sources are scans from URLscan.io and Hybrid-Analysis.com and are included included for documenting my research. PLEASE DO NOT VISIT THE WEBPAGE scanned by those sites. THE WEBPAGE RECEIVED A MALICIOUS SCORE of 97/100 on Hybrid-Analysis!! IT HAS DRIVE BY ATTACK TECHNIQUES THAT COULD INFECT YOUR COMPUTER WITH MALWARE !!!
URLScan on malicious site: https://urlscan.io/result/019ca760-3514-75db-9b22-1173be296354/#transactions
Hybrid-Analysis Scan: https://hybrid-analysis.com/sample/a80a390678266d693f3bf6d39a90f41f9837006f69b056373b25e4e594662373/69a3888bd28cc6521902e993