by Christopher Mohr
Day 98 of 100 in the 100 Days of Cyber Challenge
If you have been following along on my LinkedIn posts and here on Malware Monday you’ve seen that I have looked at several phishing campaigns recently, some targeting accounts I have like my email and sites like Fiverr.
This led me to use tools like URLScan, Hybrid-Analysis, Any.run, PhishTank and other online sandboxes that allow researchers to analyze suspicious sites more safely.
I came across a phishing attempt from the website PhishTank that has some interesting characteristics worth analyzing (the report can be found here). The webpage is located at http://bancaribeconexion.wuaze[.]com. If that URL looks unusual you’re right to be concerned.
A codepen.io rendering of the page is shown below. This is not always going to be a perfect rendering of the page, especially if it contains relative paths in style sheet references that are only valid from the site itself:
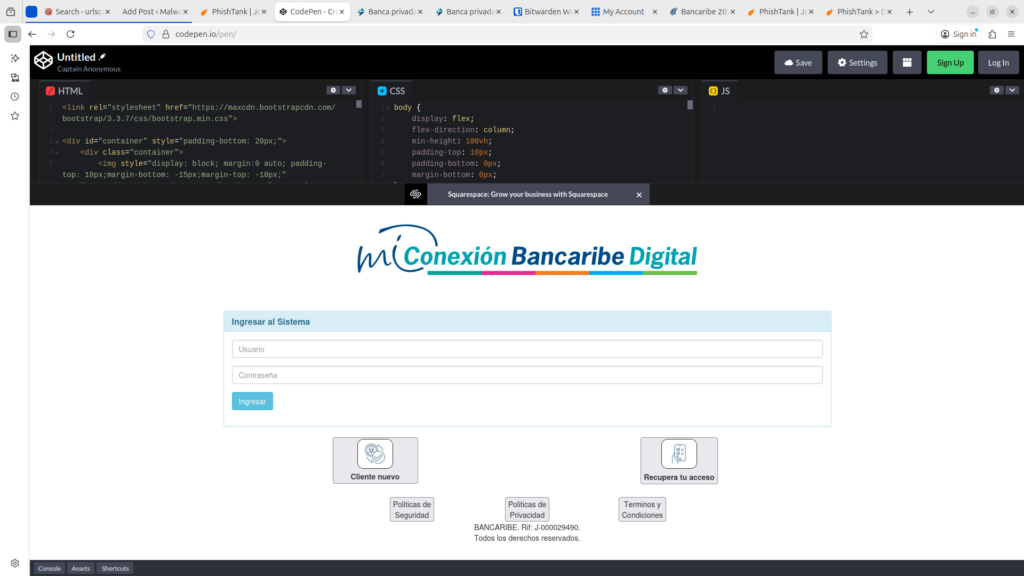
It’s Obvious the Phishing Webpage is a Copy of the Original
The HTML was obtained by scanning the page at URLscan (you can find the report here). If you choose HTTP > Primary Request > Show Report, you can see the code for the main webpage, which had these comment tags at the top:
<!– Mirrored from www5.bancaribe.com.ve/bcm/action/web/security/index by HTTrack Website Copier/3.x [XR&CO’2014], Sat, 28 Dec 2024 05:32:07 GMT –>
<!– Added by HTTrack –><meta http-equiv=”content-type” content=”text/html;charset=iso-8859-1″ /><!– /Added by HTTrack –>
On 28 December 2024 at 05:32:07 GMT, someone used a free desktop tool called HTTrack to copy the website of Bancaribe. This is a major bank based in Caracas, Venezuela with 1.2M customers as of 2018.
HTTrack can be used for legitimate uses like a developer creating an offline copy of a site. Unfortunately attackers can also use it to impersonate legitimate sites like Bancaribe’s and use them in phishing campaigns.
The attacker did not cover their tracks and remove these tags. It’s not clear whether this is because of laziness, being in a hurry, or just indifference because they knew the site was not going to be up very long.
The safe/unsafe evaluation is done at this point. We know the site is unsafe; everything else is details, but the details are revealing, so let’s continue.
The Attackers Hosted the Phishing Page on a Free Website Provider
Since the URL of this suspicious page is http://bancaribeconexion.wuaze[.]com, let’s find out more about wuaze.com.
It’s a free website page hosted by InfinityFree. If you made your own free websites back in the 1990s like I did, you may have used sites like GeoCities or Angelfire. Wuaze is the same concept.
So bancaribeconexion.wuaze[.]com is a free site (subdomain) of wuaze.com. Notice that the URL has http in the address instead of https. No publicly facing site in 2026 should be using http anymore, especially a banking page. In a modern browser with default settings http sites would cause a warning message to appear, although in fairness, many users might ignore this.
Another interesting fact is that InfinityFree as of May 2025 offered free SSL certificates to subdomains. There would be no cost to the attackers to have this feature, just some setup work.
Timeline
A look at archive.org or the Internet Wayback Machine shows that bancaribeconexion.wuaze[.]com has never been crawled, but that’s inconclusive. We don’t know why it did not scan necessarily. Is it because the page was not up for very long, or because archive.org doesn’t scan free websites so well?
The report to PhishTank was submitted Feb 23rd 2026 10:15 PM, but no time zone is specified. Current time is displayed on the site using UTC and since the most recent reports listed first show a report time close to the current time displayed, it’s safe to say the report submission time is also UTC.
Virus Total returned the following times when provided the bancaribeconexion.wuaze[.]com URL:
- First Submission 2026-02-23 22:27:50 UTC
- Last Submission 2026-02-23 22:27:50 UTC
- Last Analysis 2026-02-23 22:27:50 UTC
I could not find any timeline data outside of these times. It seems that this site was created recently, but we cannot say that with certainty. All we really know is that the page was reported recently.
How the Attack Works
It is very unlikely that any of the victims entered “bancaribeconexion.wuaze[.]com” in their browser address bar to visit the rogue login page. More than likely they received a link from a message or email and clicked it.
When the users enter their credentials, the information is sent to a server-side script 1.php. It is unwise to go to this page to investigate it. We don’t know if there is a drive-by attack waiting for us, or what might happen. We don’t have to step in front of a speeding freight train to know it’s not a good idea.
It is highly improbable that Bancaribe would host a login page on a subdomain of a free website.
What Can We Conclude?
We can be confident that this is a credential-harvesting phishing attack. Bancaribe would not set up a login page on an insecure subdomain. It was meant to target victims who are not technically savvy, who would likely ignore browser warnings about entering an http page.
The page has characteristics consistent with a pre-packaged kit containing tools for phishing attacks. The self-contained file structure with the file 1.php, the css and js directories with relative directory references in the code suggest an organized file structure that’s easier to deploy as a single unit.
InfinityFree had numerous problems with abuse occurring on wuaze.com and announced it had been suspended in May 2024 by the registry, resulting in a takedown of the domain and its subdomains. Although the suspension was lifted, the abuse, as demonstrated by this blog article, has resumed. If you encounter a phishing site hosted on a wuaze.com subdomain you can report it directly to InfinityFree at report-abuse@infinityfree.com.